Real-World Scenario: A Small Mistake With Big Consequences
Recently, Binary City experienced an internal security incident that highlights how small everyday decisions can create serious risks for the company.
During routine work on-site, a contractor requested internet access. An employee, wanting to be helpful, shared the password to the company’s “BCityDevice” Wi-Fi network.
At first glance, this seemed harmless. The intention was simply to help the contractor to stay connected.
However, this network was not intended for external access.
Because the password was shared, the contractor’s device was able to connect to an internal network that is intended only for the use by authorised staff. In the wrong circumstances, a person with the right technical knowledge could potentially use such access to:
- Explore internal network resources
- Attempt to access company systems
- Identify vulnerabilities within the network
- Launch further attacks against company infrastructure
Fortunately, this situation was identified before any damage occurred. However, it clearly demonstrated an important lesson: Even well-intended actions can unintentionally expose the company to risk.
This is why security procedures exist.
They are not designed to slow down work or make things difficult. Instead, they ensure that:
- Access is granted safely
- Systems remain protected
- Sensitive information is not exposed
Most security incidents do not happen because someone intended harm.
They happen because someone was trying to help, move quickly, or solve a problem.
This training module is designed to help everyone recognise these situations and know what the correct action should be.
Remember: Security starts with everyday decisions.
Introduction
Information security is not only the responsibility of the IT team (Systems Administration) or management. Every Binary City employee plays a role in protecting Binary City’s systems, data, clients, and reputation.
Most security incidents worldwide are not caused by advanced hackers or complex technical attacks. Instead, they are often the result of simple everyday mistakes, such as:
Sharing network access with the wrong person
Leaving devices unlocked
Accidentally sharing sensitive information
Allowing unauthorised people access to secure areas
These mistakes are rarely intentional. However, even small oversights can create serious risks for the organisation.
This training module focuses on practical, real-world behaviour that helps prevent these situations. The goal is to make sure that every employee understands:
- How everyday actions affect security
- How attackers exploit small mistakes
- What you should do in common workplace situations
By the end of this module, you should feel confident about how to protect Binary City in your day-to-day work.
Why Small Mistakes Create Big Risks
Many security incidents begin with something small.
Examples of everyday mistakes include:
- Sharing a Wi-Fi password with someone who should not have access
- Sharing passwords without utilising a tool like 1Password.
- Writing down passwords
- Leaving confidential documents visible on a desk
- Leaving a computer unlocked when stepping away
- Providing internal information to someone without verifying who they are
Attackers often look for these small gaps because they are easier to exploit than complex technical vulnerabilities.
For example: An attacker may pretend to be a contractor or visitor and ask for network access.
If they receive access to the wrong network, they may be able to:
- See internal systems
- Access sensitive information
- Attempt further attacks on company infrastructure
This is why we emphasise the principle: “A company is only as secure as its employees.”
Each employee’s actions help protect the organisation.
Stop & Think...
Think about your normal workday.
Have you ever:
- Shared information quickly to help someone?
- Left your desk without locking your computer?
- Helped a visitor or contractor by giving them access to something?
These actions are usually done with good intentions.
However, attackers often rely on exactly these situations.
Question: What small action in your daily routine could unintentionally create a security risk?
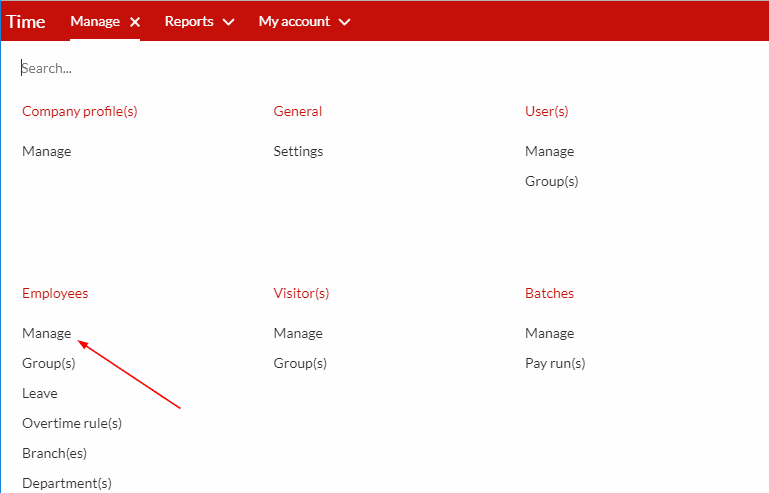
Network Access & Wi-Fi Security
Binary City uses different networks for different purposes. These networks are separated to protect sensitive systems.
These include:
- Internal company network
- Guest network
- Testing network
- Device network
These networks are not interchangeable, and access must be carefully controlled.
Important Rules
Employees must never share company Wi-Fi passwords with:
- Contractors
- Visitors
- Clients
- External vendors
- Anyone not authorised to access the network
- Staff members (each staff member must authenticate with their own credentials)
Even if someone appears trustworthy, network access must always be approved through the proper process.
If someone requires internet access:
- Direct the visitor to reception
- A guest WiFi voucher will be provided to the visitor to allow access to our guest network
This ensures the person receives only the access they require, and nothing more.
Handling Visitors, Contractors & External Parties
Binary City regularly works with contractors, suppliers, and visitors.
While these relationships are important, they must be managed securely.
Employees must never:
- Provide system access independently
- Share network credentials
- Allow a visitor to use a network cable to go onto our networks
- Allow visitors into restricted areas unsupervised
- Share internal information without authorisation
Correct process
Never share the passwords for our internal company networks with anyone who is not explicitly authorised. This includes:
- Contractors
- Visitors
- Clients
- External vendors
Visitors and guests may use the designated Guest Wi-Fi. This network only provides access to the internet and does not give access to internal systems or company data.
If someone requests network access beyond the Guest Wi-Fi:
- Do not grant it yourself
- Follow the proper escalation procedures (contact your manager or the System Administrator)
- Always verify that access is necessary and approved
Remember: Using the Guest Wi-Fi correctly keeps our systems secure while still allowing visitors to work online safely.
Stop & Think...
Imagine the following situation:
A contractor working on-site asks you for the Wi-Fi password so they can download
something quickly.
They seem legitimate, and the request appears harmless.
Ask yourself:
- Do I know which network they would connect to?
- Do I know what access that network provides?
- Do I have the authority to grant that access?
Remember: Even small access permissions can expose internal systems if handled incorrectly.
Sensitive Information Handling
Binary City employees often work with internal and confidential information.
Examples include:
- Customer information
- Internal reports
- Financial data
- Client employee and clocking data
- Client sensitive data
- Technical system information
- Source code or development data
This information must never be shared casually.
Before sharing any information, always ask:
- Who is requesting this information?
- Are they authorised to receive it?
- Is there a secure way to share it?
If you are unsure, always ask your manager first.
Never assume information can be shared simply because someone asks for it.
Stop & Think...
Before sharing any information, pause and ask yourself three questions:
- Who is requesting this information?
- Are they authorised to receive it?
- Would I be comfortable if this information became public?
If you cannot confidently answer these questions, stop and verify first.
Clear Desk & Clear Screen Behaviour
Physical security is just as important as digital security.
Even in trusted environments, information can be exposed if employees are not careful.
Clear Desk
When leaving your workspace:
- Store sensitive documents in drawers or cabinets
- Do not leave confidential information visible
- Remove notes that contain passwords or sensitive information
Should you require guidance on the appropriate storage location for your devices, documents, and other items, please contact your manager for assistance.
Clear Screen
When leaving your computer:
- Lock your screen
- Ensure no sensitive information is visible
- Prevent unauthorised viewing of your screen
This is especially important in shared workspaces or open offices.
Stop & Think...
Imagine someone walks past your desk while your computer is unlocked and sensitive information is visible on your screen.
Even if they do nothing malicious, they could accidentally see:
- Client information
- Internal reports
- System details
Question: Would your current workspace pass a Clear Desk and Clear Screen check right now?
Device & Workspace Security
Many employees work with laptops, mobile devices, and other equipment.
These devices often contain sensitive information or company system access.
Important rules
Employees must:
- Never leave devices unattended in public places
- Keep devices physically secure
- Use passwords and screen locks
- Protect login credentials
If a device is lost or stolen, it must be reported immediately to the IT team and your manager.
Security for Remote Workers
Binary City supports remote work for employees located across Namibia and South Africa, as well as occasional remote work by HQ staff.
Working remotely requires extra awareness of security risks. To make it safe, Binary City uses special tools on company devices:
- Trellix on Windows devices
- Iru on Mac devices
These tools help protect your device automatically by:
- Checking for malware or viruses
- Keeping your software up to date
- Ensuring your device follows company security rules
This means you don’t need to be a tech expert to keep your work safe, but you do need to follow some basic rules.
What staff must do when working remotely
Device safety:
- Only use your company-assigned device. Do not let family, friends, or others use it.
- Lock your device whenever you step away, even for a short time.
- Keep your device in a safe place when not in use. For example:
- At a coffee shop, don’t leave it on the table unattended.
- At home, don’t leave it on a couch or desk where visitors might have access.
- Be careful when traveling, don’t leave your laptop visible in a parked car.
Using Wi-Fi:
- Home Wi-Fi:
- Binary City’s tools (like Trellix and Iru) help protect your device even if your home Wi-Fi isn’t perfectly secure. You don’t need to worry about configuring your network.
- Public Wi-Fi:
- Often okay to use in Namibia and South Africa for general work. These networks may track user behavior, so avoid entering sensitive passwords or banking information when using public Wi-Fi.
- If possible, use a password-protected Wi-Fi network, or a mobile hotspot if you are unsure of the network.
- Check website security:
- Only access websites that are secure. A secure website uses encryption to protect the information you enter (like passwords or personal data). You can check this by looking at the address in your browser:
- It should start with https:// (the “s” stands for secure)
- You may also see a padlock icon next to the web address
- Avoid websites that do not have HTTPS or a padlock, especially when entering sensitive information like company accounts, banking, or personal details.
Mind your surroundings:
- Be aware of who can see or hear your work. Examples:
- Don’t discuss sensitive company information loudly in public or shared spaces. Noise-cancelling headphones are prone to make the user unaware of how loud they talk.
- Be mindful of “shoulder surfing”, where someone is looking over your shoulder to see your screen. This can happen in coffee shops, airports, or even at home if visitors are around.
Stop & Think...
Before you start working remotely, pause and ask yourself:
- Is my device secure and only being used by me?
- Have I locked my device when stepping away?
- Am I aware of my surroundings? Can someone see or hear what I’m working on?
- If I’m on public Wi-Fi, am I avoiding sensitive logins or transactions?
Remember: Remote work must follow the same security standards as working in the office. Binary City’s protection tools keep your device safe, but your awareness and good habits are the key to keeping company data secure.
When Something Feels Wrong
Sometimes situations may feel unusual or suspicious.
Examples include:
- Someone asking for information they should not need
- Someone asking for system access unexpectedly
- Suspicious emails or messages
- Unauthorised persons in restricted areas
If something does not feel right: Trust your instincts.
Our employees should never feel uncomfortable reporting concerns.
Reporting Concerns
If you suspect a security issue:
- Report it to your manager
- Report it to the System Administrator
- Report it to the ISMS Officer
- Log an incident on our Intranet
- Do not attempt to fix the issue yourself
Early reporting allows the company to respond quickly and prevent damage.
Remember: “When in doubt, escalate.”
It is always better to report something that turns out to be harmless than to ignore a real issue.
Role-Based Scenarios
The following examples show situations employees may encounter.
Scenario 1 – Contractor Request
A contractor asks you for the office Wi-Fi password so they can download files.
Correct response:
- Do not share the password.
- Contact reception to arrange proper network access.
Scenario 2 – Visitor in a Secure Area
You notice a visitor standing near company equipment without supervision.
Correct response:
- Politely ask who they are visiting and notify the responsible employee or manager.
Scenario 3 – Unknown Information Request
Someone emails asking for internal documents and claims to be working with another department.
Correct response:
- Verify the request with the department or manager before sharing anything.
Scenario 4 – Unlocked Computer
You notice a colleague’s computer is unlocked while they are away.
Correct response:
- Lock the computer and inform the colleague so they can avoid the mistake in the future.
- Although it may be amusing at the moment, do not post messages on the company’s communication channels, pretending to be the employee.
- Report the incident.
Assessment
At the end of this module, employees must complete a knowledge assessment quiz.
The quiz will include scenario-based questions designed to confirm that the training has been understood.
Examples of questions include:
- A contractor asks for the office Wi-Fi password. What should you do?
- You notice confidential documents on a desk after hours. What is the correct action?
- Someone requests internal information but you are unsure if they are authorised. What should you do?
Pass Requirement
To successfully complete this training:
- Employees must achieve a minimum score of 90%.
If the pass mark is not achieved, you must review the training and retake the quiz.
This requirement ensures that all our employees understand their responsibilities and helps maintain a strong security culture across Binary City.
Stop & Think – Final Reflection
Before starting the quiz, take a moment to reflect: Security incidents rarely happen because someone intended to cause harm.
They happen because someone:
- Wanted to help
- Was in a hurry
- Assumed something was safe
The goal of this training is simple: Pause. Think. Verify.
Small decisions made every day protect Binary City’s systems, clients, and reputation.
👉 Click here to start the ISMS quiz
Final Message
Security is not just about systems and technology.
It is about people making the right decisions every day.
Each employee plays an important role in protecting:
- Our colleagues
- Our clients
- Our systems
- Our reputation
Security starts with you.